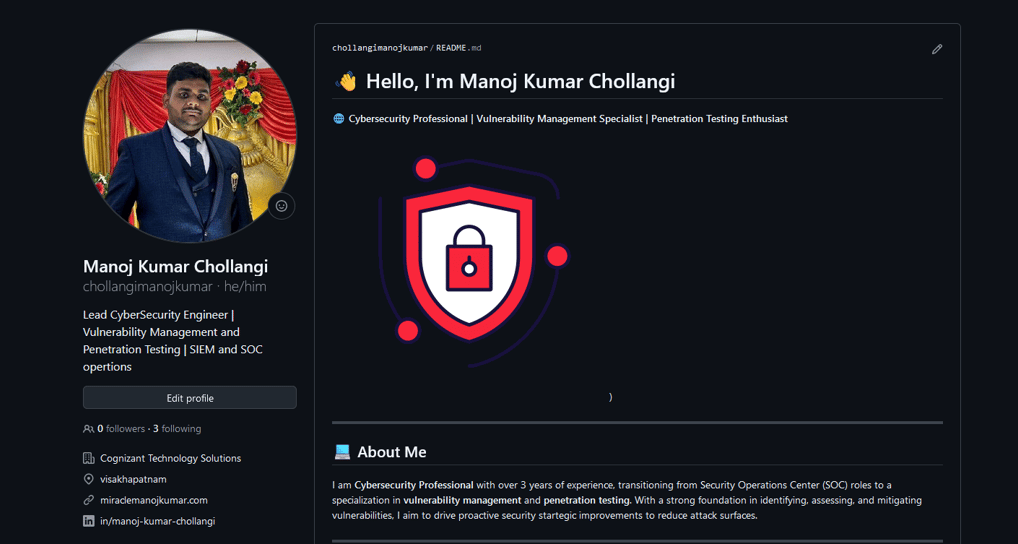
Cybersecurity Portfolio
Showcasing my skills in cybersecurity operations and management.


Security Operations
Administration and monitoring of security operations effectively.


Vulnerability Management
Identifying and mitigating vulnerabilities in systems and applications.




Reporting Insights
Detailed reports on security incidents and vulnerabilities.
Project Overview
Comprehensive overview of my cybersecurity projects and skills.
→
→
→
→

Gallery
Showcasing my cybersecurity skills through various project highlights.










Cybersecurity Services Offered
Expertise in security operations, vulnerability management, and comprehensive reporting for enhanced protection.
Security Operations Management


Administration and monitoring of security operations to ensure optimal cybersecurity performance.




Vulnerability Assessment Services
Identifying and managing vulnerabilities to safeguard systems and data from potential threats.
Detailed reporting on security metrics and incidents to inform strategic decision-making.
Comprehensive Reporting
Skills
Qualys Vulnerability Management,
Penetration Testing
Nessus,
SIEM and SOC
Email Analysis, Phish ER
XDR, XSIAM, Endpoint Detection and Response
Darktarce
CONTACT
Focus
chollangimanojkumar@gmail.com
© 2024. All rights reserved.
